Zero Trust Architecture for Enterprise Data Pipelines
Supaflow is built with security at its core. Customer data never leaves your environment—only metadata is stored in Supaflow Cloud, encrypted with customer-managed keys.
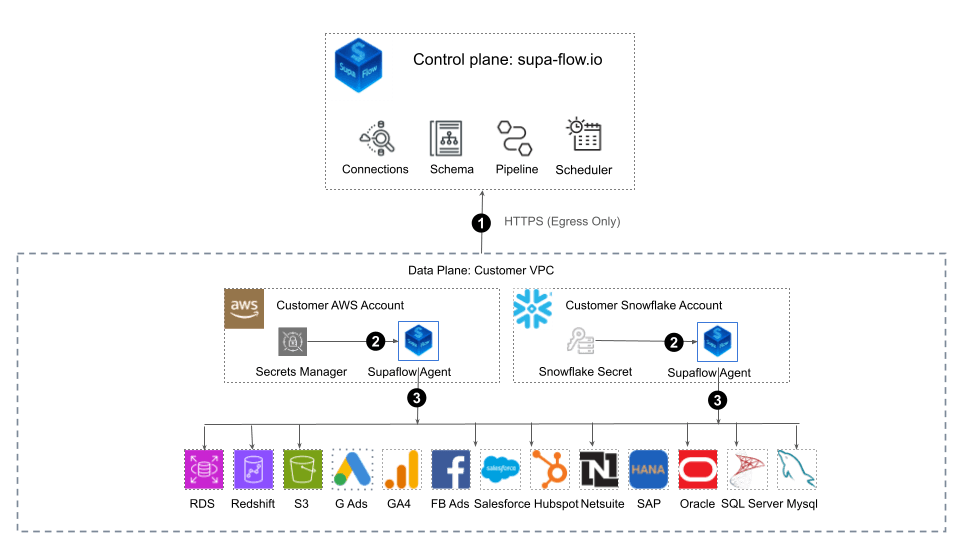
Supaflow uses a strict control-plane / data-plane separation. Agents run entirely within your AWS account or Snowflake Snowpark Container Services (SPCS) and communicate with Supaflow exclusively via outbound HTTPS polling. No inbound firewall rules, IP allowlists, or SSH access are required.
Data flows directly from source to destination, without passing through Supaflow infrastructure.
What This Means in Practice
The security model on this page is designed to answer the questions infrastructure and compliance teams usually ask first: network direction, data residency, and key control.
No inbound access required
The Supaflow Agent polls for work over outbound HTTPS only. The security model does not depend on inbound firewall rules, SSH sessions, or IP allowlists.
Customer data stays in the data plane
Raw customer data and PHI stay in your environment or in Snowflake compute. Supaflow Cloud stores orchestration metadata and encrypted connection metadata, not the business data flowing through jobs.
Customer-managed keys stay with you
The agent decrypts job metadata locally using private keys stored in your own secret manager, so Supaflow does not need access to the keys used to unlock sensitive credentials.
How Supaflow Agent Works
Data flows directly from source to destination—no middlemen.
Agent Polls for Jobs
The Supaflow Agent runs in your AWS environment or Snowflake SPCS and polls Supaflow for work using outbound HTTPS only. No inbound network access is required.
Agent Decrypts Job
The agent retrieves encrypted job metadata and decrypts it locally using customer-managed keys stored in your secret manager (AWS Secrets Manager or Snowflake Secrets).
Agent Runs Pipeline
The agent connects directly to your sources and destinations within your network. Data moves from source to destination without ever touching Supaflow Cloud.
Enterprise Security Features
Zero Trust Architecture
No ingress connections required. Agent polls control plane via HTTPS egress only, ensuring your network perimeter remains secure.
Customer-Managed Encryption
Your private encryption keys stay in your Secret Manager. We never have access to decrypt your sensitive connection credentials.
Data Plane Isolation
All customer data processing happens in your VPC or Snowflake SPCS. Raw data and PHI never transit through Supaflow infrastructure.
Metadata-Only Storage
Supaflow stores only pipeline configurations, lineage, and encrypted connection metadata—never your actual business data.
Per-Tenant Encryption
Dedicated encryption keys per tenant ensure complete data isolation. Each tenant's metadata is encrypted independently with keys they control.
Audit Logging
Track pipeline configurations, job executions, and user actions for compliance reviews and operational visibility.
Metadata Residency & Compliance
Lives in Supaflow Cloud
- •Pipeline configurations
- •Lineage metadata
- •User and workspace settings
- •System orchestration data
- •Connection credentials (encrypted with your public key)
Stays with You
- Encryption private keys
- Raw data and PHI
- Execution logs and artifacts
- Sensitive business information
Compliance-Friendly Architecture: Because customer data remains in your environment (or Snowflake compute), this architecture often eliminates the need for a Business Associate Agreement.
Flexible Deployment Options
AWS VPC Deployment
Deploy Supaflow Agent in your AWS account with full control over networking, IAM, and compute resources. No firewall rules or SSH bastions needed—agent uses standard HTTPS egress.
Snowflake SPCS Native
Run the agent natively in Snowflake Snowpark Container Services for ultimate data gravity and security. Zero infrastructure setup required.
Learn how Snowflake native ETL works →
Watch how to deploy the Supaflow Agent in Snowflake SPCS in minutes
Additional Security Controls
Role-Based Access Control (RBAC)
Strict identity and access management boundaries at workspace and project levels.
Audit Trail
Track pipeline configurations, deployments, and user actions for compliance and operational reviews.
Encryption in Transit & At Rest
Industry-standard TLS encryption for all network communication. Metadata encrypted at rest in our database.
Frequently Asked Questions
Common questions from teams evaluating network, key management, and deployment requirements.
Does customer data pass through Supaflow Cloud?
Does Supaflow require inbound firewall rules or SSH access?
Where do encryption keys live?
Where can the Supaflow Agent run?
Ready to secure your data pipelines?
Start building with Supaflow's zero trust architecture today.